Please stop exposing API keys to all admins in webhooks pages [Update: It's a different key!]
Answered
Posted Aug 24, 2022
Edit: It's not the token for Basic Auth like I thought! I didn't want to be "rude" and try to test the API with what I thought were a coworker's exposed credentials, but that would've done the trick to tell.
Hi,
This is a security issue. As a user with permission to edit webhooks, you've now given me an option to "reveal" the secret key that is set on those webhooks. These aren't my keys. I have no business being able to see them. This is essentially giving me free reign to impersonate other admins on the account via the API. I essentially have a set of passwords for other accounts. You aren't able to see the key you generated again once you leave the API page. Why are secret keys being exposed on this page?
1
2

2 comments
Official
Chris Sos
Hi CJ,
Thanks for your post. This article on our developer documentation may assist understanding the purpose of the signing secret: Verifying webhook authenticity
The TL;DR is that this key is used by Zendesk to sign each individual webhook request. The receiving server can validate the signature in the header to verify that the request indeed came from Zendesk. It can also be used to prevent replay attacks against your server if your request is somehow hijacked.
This secret key is not a credential and we do not recommend using it as such, it is provided for users who would like an extra layer of security and validation on requests. For authentication, we recommend utilising the authentication methods provided on the webhook (Basic Auth or Bearer token at this time).
Hope this helps!
Chris
0
CJ Johnson
Oh thank GOODNESS. I didn't look super closely, and the labeling is very vague.
Shots below are not my prod account info, I wanted to make super sure on my d3v instance.
I went ahead and made a new API token and new webhook.
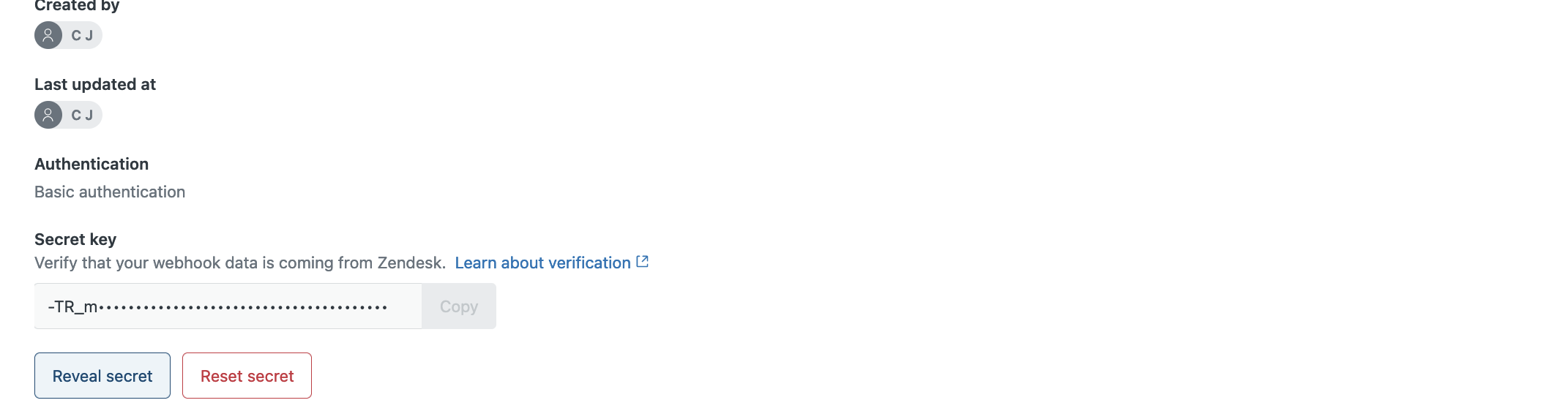
You can see that it really looks like you are showing the "secret key" for the Authentication in the view:
I assumed that the key being hidden was the token I literally entered in for basic auth via token, one step earlier in making the webhook. The help text, "verify that your webhook data is coming from Zendesk", even fits the misunderstanding of what this field is, I'm doing a PUT/POST, so I'm pushing the data, that would be me and my zendesk credentials that are being checked, right? (Wrong!)
I'm VERY glad that this is not showing the API tokens.
However, I still feel this is pretty undesirable/not super secure, as your own documentation has the following to say about it:
Note: The secret key should be treated like any other credential and should not be committed to code or exposed publicly.
0
Sign in to leave a comment.